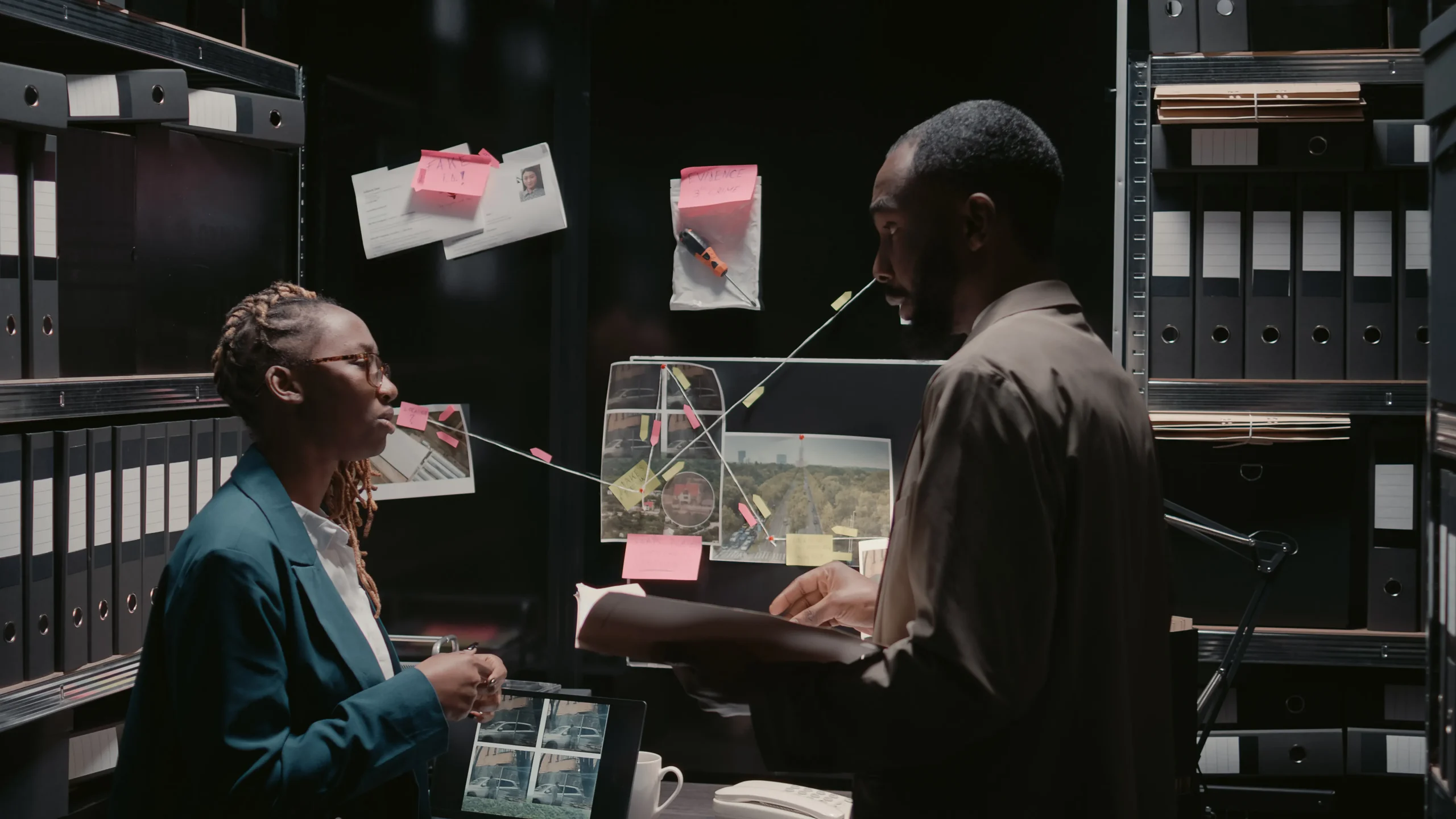
Asset Tracing
Asset tracing is the systematic process of identifying, locating, and tracking assets that have been hidden, misappropriated, or unlawfully transferred. It also involves establishing ownership links between assets and individuals or organizations.
Riskhouse International: Protecting Your Interests
In today’s fast-moving and increasingly complex business environment, risks are often hidden beneath the surface. Fraud, undisclosed liabilities, reputational exposure, and concealed assets can quietly undermine financial stability and erode trust.
Cupid’s dark side: How to spot “pig butchering” crypto scams this Valentine’s Day
Valentine’s Day is a celebration of love, connection, and the hope of finding someone special. But in today’s digital world, not every “perfect match” is what they seem.
Uncover the truth, secure the cloud
In today’s data-driven world, cloud technology powers efficiency, flexibility, and growth but it also introduces new risks. At Riskhouse International, we provide Digital Forensic Investigation for Cloud Servers to help organizations uncover digital evidence, trace cyber incidents, and safeguard their data
Trace every threat, strengthen your network
Your network is the foundation of your digital operations; carrying critical data, communications, and transactions every moment. As cyber threats grow in sophistication, even one breach can disrupt operations and damage trust.
The Anti-Money Laundering and Combating of Terrorism Financing Laws (Amendment) Act 2025: Is your Business Ready for March 2026?
Starting March 2026, the Anti-Money Laundering and Combating of Terrorism Financing Laws (Amendment) Act 2025 will be fully effective. This act applies to many everyday businesses, such as Betting and Mining, Professional services such as accounting, real estate and even the Public Benefit Organizations (PBOs).
Artificial intelligence (AI) in credit risk assessment and scoring for financial institutions in Kenya
Artificial Intelligence (AI) and Machine Learning (ML) are rapidly transforming Kenya’s financial sector. The March 2025 Central Bank of Kenya (CBK) survey on Artificial Intelligence (AI) in the Banking Sector shows that 65% of financial institutions adopted AI for credit risk assessment, making it the most common application.
Digital Credit and Data Protection in Kenya
In Kenya, the creation of digital credit apps has opened access to small-loans for many who are under-banked. However, alongside this growth have come serious concerns about misuse of personal data, unethical recovery practices, and breaches of privacy rights.
Policy review and development: From policy gaps to strategic growth
Policies are more than compliance checklists, they are strategic tools that protect your organization, guide decision making, and turn potential risks into growth opportunities.
The risk of social media cryptocurrency scams in Kenya despite VASP regulation
Kenya’s recent enactment of the Virtual Asset Service Providers (VASP) Bill into Law marks a milestone in regulating the crypto industry. The law imposes clear obligations on Virtual Asset Service Providers (Exchanges, Custodians, Brokers, Investment Advisors, Initial Coin offering providers), including licensing, capital requirements, cybersecurity, AML/CFT compliance and consumer protection, with regulatory oversight from the CBK and CMA.